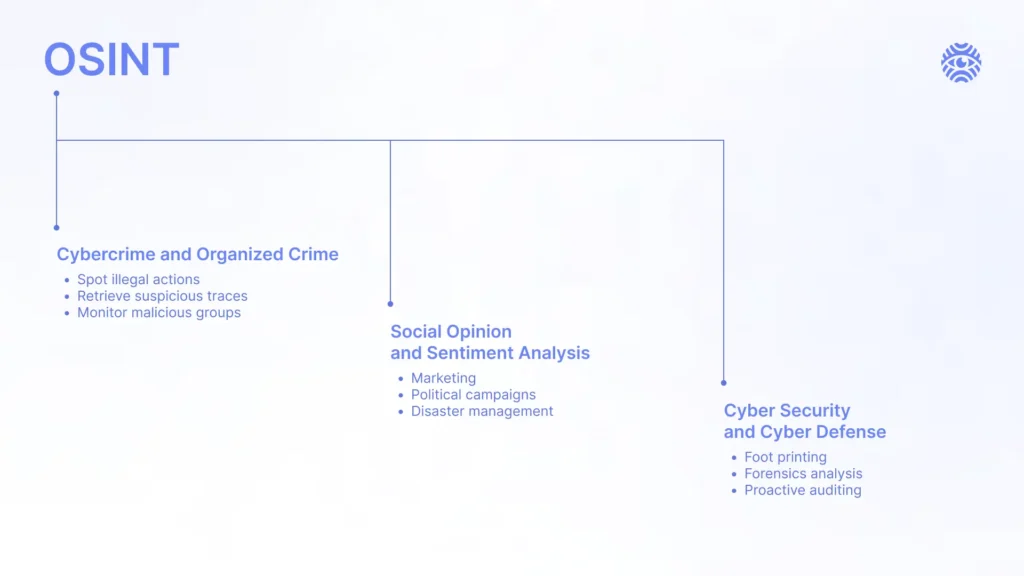
OSINT is a useful strategy not just for investigations and studying others’ networks but also for securing an organization’s protection. The benefits of OSINT in cybersecurity are multifaceted: finding culprits, testing the strength of the system and preventing hacker attacks, among others. Learn how your company can win big time by investing in OSINT as a part of the digital defense with this quick guide.
How Is OSINT Used in Cybersecurity?
The organization can boost its cybersecurity standing by borrowing methods and approaches from OSINT investigations. OSINT is used to gather threat intelligence information on potential threats, including details about threat actors, their tactics, techniques, and procedures. Moreover, OSINT is crucial in assessing an organization’s online presence and vulnerabilities, helping to identify gaps that could be exploited. In this way, digital security teams can understand the thought process of hackers, know about emerging hazard trends as well as adjust the system protection accordingly. Now, let’s dive deep into specific ways in which OSINT tactics can be useful for your organization.
Cybersecurity OSINT Enables Companies to Use:
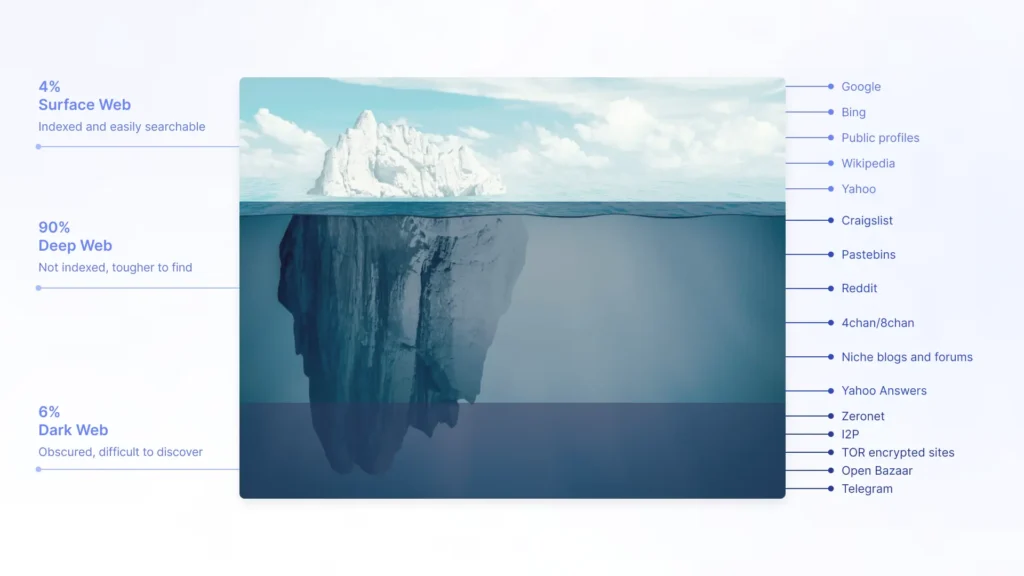
Dark Web OSINT
Many secrets of the web are available only if you search for sites hidden from the public eye. OSINT tools can be used to explore dark web content, such as databases, directories and other resources that aren’t indexed by traditional search engines. Dark web OSINT serves as an early warning system for cybersecurity incidents. OSINT analysts monitor dark web forums and communities where illegal activities, discussions and transactions often take place. That’s how the company’s cybersecurity team can either prevent preplanned attacks using threat intelligence or find out the culprits who might have discussed their intentions with others.
Code Repositories
Code repositories, such as GitHub or GitLab, host a vast amount of open-source and private code. It makes these archives valuable sources for cybersecurity professionals seeking to understand the software’s or application’s protection level. For example, automated tools and manual analysis are often employed to identify security issues in the code, such as outdated libraries, insecure coding practices or exposed API keys. That’s how cybersecurity OSINT pros take advantage of code repositories to fill in the safety gaps and then learn from their mistakes with threat intelligence.
Geoint
GEOINT is a branch of OSINT focused on retrieving location-based information and analysis to collect threat intelligence and enhance the understanding, prevention, and response to cyber threats. Here is how information about location can be useful for cybersecurity:
- Know the Origin of the Culprits With OSINT. GEOINT can help identify the geographical origin of cyber attacks by analyzing the locations of IP addresses, network traffic and other relevant indicators. That’s how you know where to look for answers in case criminals penetrate the system.
- Handle the Forensic Investigation. Being aware of when and where specific activities occurred helps in reconstructing the incident and improving forensic analysis. The cybersecurity OSINT team will benefit from this knowledge to strengthen certain parts of the security network.
- Manage a Supply Chain. The elements of GEOINT are valuable for mapping and analyzing the geographical distribution of elements within the supply chain. This OSINT threat intelligence data is crucial for assessing and mitigating risks related to the cybersecurity of the supply chain.
What Security Threats Does OSINT Protect From
Moreover, the OSINT cybersecurity data can protect the organization’s system from a plethora of common threats. Consider the following hazards:
OSINT, Google Dorks, Targeted Cyber Attacks
The point of such attacks is to use OSINT Google Dorks as a means to get into the system and exploit its vulnerabilities. For instance, attackers use Google Dorks to find exposed sensitive information, misconfigurations, or weaknesses on websites or apps. These pathways might reveal specific cybersecurity OSINT info like file location, login pages or directories that can be targeted for exploitation. It is crucial to prepare for such attacks with threat intelligence OSINT data to have a working scenario in case the culprits target the company’s system.
Social Engineering
The goal of social engineering is to take advantage of the human factor to find the cybersecurity gaps. Learn some of the most popular social engineering strategies used by the hackers:
Doxxing
Such intrusions focus on manipulating and exposing certain individuals with OSINT more than seeking the vulnerabilities of the cyber defense barrier. The intent of the criminals is to research, collect, and publicly reveal private information about an individual without their consent. The person can be blackmailed by the doxxed data or suffer from harm, harassment and embarrassment once it is exposed. Doxxing may involve manipulating individuals or impersonating them to gather additional information, such as through phishing attacks or pretexting, in order to hack the organization. That is why companies need cybersecurity OSINT to hire only reliable candidates with no controversial digital footprint and prepare employees on how to act if they get doxxed.
Phishing Attacks
Similarly to doxxing, phishing attacks are about aiming at specific individuals using the OSINT tools. However, hackers who do phishing use deceptive tactics to trick people into providing sensitive information, such as login credentials, financial details or personal information. Typically, criminals send victims fraudulent emails, messages or websites that appear to be from a trustworthy source to make the person open them up. After that, hackers gain access to the device to penetrate the organization or steal the user’s personal data. Knowledge of the cybersecurity OSINT basics and digital literacy practices to avoid being tricked.
Best OSINT Cybersecurity Tools
If you want to implement cybersecurity OSINT practices in your organization, use these tools that simplify and automate the process.
Use X-Ray Contact for Threat Intelligence
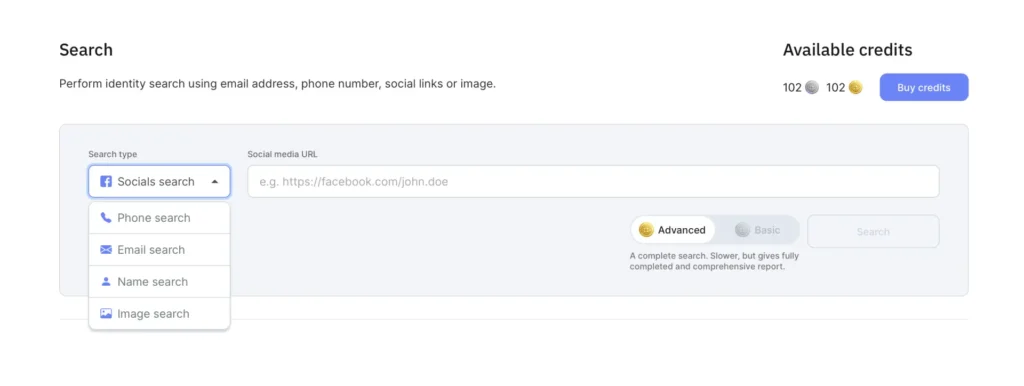
X-Ray Contact is a convenient data aggregation instrument that you can use to prevent attacks based on social engineering. You can utilize the OSINT tool in order to check for the previous online footprint of people who are about to enter the system. That is how organizations find out whether they hire a reliable candidate. The search goes with just a few easy steps:
- Tap on the “Platform” tab in the heading of the X-Ray Contact website.
- Insert any information you have on the suspicious person, such as Name, Email, Photo or even a Socials link.
- In case the person is in the X-Ray Contact’s database, receive an OSINT report with all information available on the person, including even location, education, previous work experience, age or relatives. That is how an organization can create a comprehensive Search Profile before allowing an individual to get into the system.
Maltego
The OSINT tool is useful for figuring out the potential and nature of the attacks through such data as domain names, IP addresses and network infrastructure. Maltego can be integrated with various threat intelligence feeds to enrich its dataset.

Babel X
The main feature of the Babel X OSINT instrument is verifying input information through a variety of different sources to find a match. Babel X can aggregate OSINT information from a wide range of online sources, helping cybersecurity professionals collect threat intelligence data from all over the Internet to boost system security.
Conclusion
Since most OSINT tools are available online for a reasonable fee, don’t miss out on the possibility of enhancing cybersecurity and getting threat intelligence data.


