

Today, you need just the Internet to do things that even the largest intelligence agencies could not even dream of a few decades ago. Even though these agencies had impressive budgets (but no software for OSINT).
For the first time, the military and intelligence services used the term OSINT (Open-Source Intelligence) to refer to collecting strategically important but publicly available information in national security matters. The Internet, social media, and digital services opened up vast opportunities to collect information about the IT infrastructure of an organization and its employees.
Now we take all this software for OSINT for granted. For example, we have access to the “darknet,” where people who are not engaged in the most legal activities live. Or high-resolution satellite images and interactive maps that allow us to find out how the place looks physically in a few clicks. Of course, social networks are where we can find almost any information about a person.
All these new features and new open-source data types have given researchers a much simpler way to solve their problems, and this way is called OSINT.
OSINT in cyber-security
Wikipedia defines OSINT as “the collection and analysis of data gathered from open sources (overt and publicly available sources) to produce actionable intelligence.”
OSINTs are actions that are available to anyone with Internet access. So, if you’re reading this right now, you can do it too.
People who know how to apply logic and connect the dots can understand and learn many things that others would rather hide. Few people think about it, but the amount of information we can find in the public domain is staggering.
Hackers often start their attacks from the so-called passive reconnaissance phase.
The first step is to get to know the users or target systems of their interest. Information collection is carried out without active interaction with the object of study.
For example, attackers can turn to publicly available sources, such as social networks and public pages of employees, to learn more about how a company works from the inside. They also can collect information from satellites, public cameras, and street shots to understand more about the organization.
Understanding how OSINT tools can be used will help you analyze and identify publicly available information about you or your organization on the web. Sometimes this simple action can help you avoid big problems before hackers can take advantage of it.
3 categories of software for OSINT
Finding a company’s assets information
Today, the vast majority of companies have publicly available information about the infrastructure, both external and internal. OSINT tools will help you find such by yourself or with the help of a specialist, report, and decide whether attackers can use it.
You should take into account that searching for information using OSINT tools does not imply active exploration and direct interaction with systems.
Discovering sensitive information from external sources
Employees are another source of information about your company and its internal processes. People don’t suspect that they provide a stalker with another piece of the puzzle by posting tweets or messages on social networks about completed projects, congratulating colleagues on a product’s launch, or a successful deal.
For instance, an employee who finally closed a tough deal might boast on Facebook: “Colleagues, we finally did it! The contract is signed. It’s time to celebrate.” This information is gold for hackers and competitors who understand what kind of contract they are talking about.
In this way, OSINT tools help you find confidential information outside your organization by using social media posts, articles, and websites unrelated to your company.
Aggregating information
After discovering and collecting all the publicly available information, you need to use the OSINT tool that will combine it into a single picture and analyze it. Such tools not only collect information from publicly available sources but can also bring all the pieces of the puzzle together.
You will be able to answer the most important questions with the help of these tools: What? Who? Where? Why?
These are automated programs that can scan globally, adaptable tools that can filter out irrelevant data, systems that can query data from various devices, and so on.
10 best tools and software for OSINT
We have prepared a list of the ten most useful tools in our opinion, as well as described the pros and cons of the software for OSINT. Which of these tools to use is up to you. There are paid and free versions so that everyone can choose what suits them best.
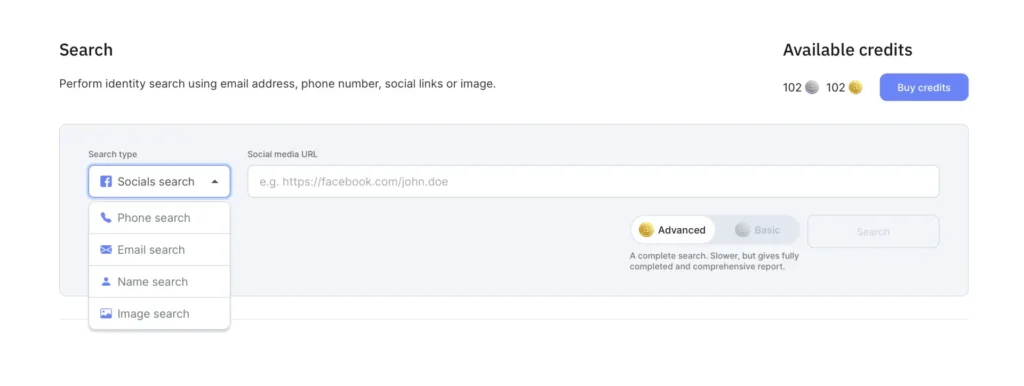
X-Ray Contact
It’s an entry-level OSINT tool that you can use just in a few clicks. Due to X-Ray Contact’s UX design, it can be exploited even by people with no prior investigation experience. The gist of the instrument is aggregating data from different databases to provide a detailed Person Profile if they are present in the sources.
Link to the official site – https://x-ray.contact/
Pros:
- Intuitive design
- Beginner-friendly tool
- Rich database sources
- Provides convenient reports
- Has a variety of packages and subscriptions based on your needs
- Suited for both PC and mobile searches
Cons:
- Mostly not free to use
Price: Has a detailed price list with different options, from a free trial to $179.99.
Recon-ng
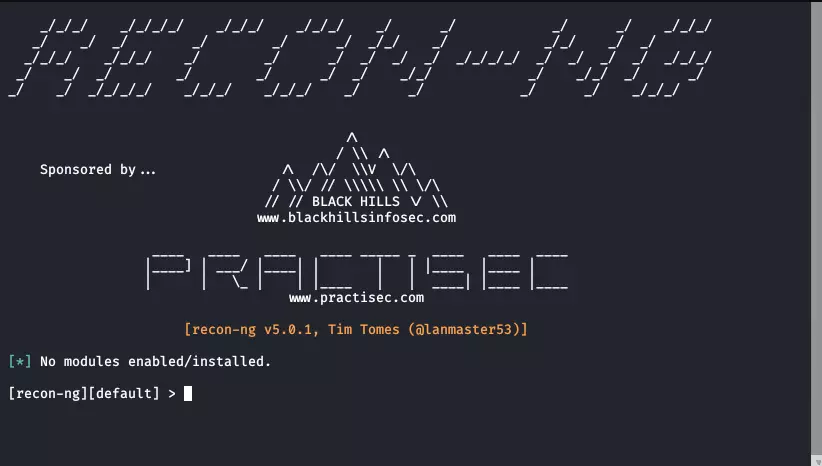
Recon-ng is a fully-featured web intelligence software platform based on Python. It has independent modules, simple database interaction, built-in functions, interactive help, etc. Recon-ng provides a convenient and powerful environment where OSINT can be done quickly and thoroughly. In fact, one of the best programs for OSINT.
Link to the official site – https://github.com/lanmaster53/recon-ng
Pros:
- Support for any operating system
- Big community
- Easy-to-use interface
- Open source
- Free
Cons: Rather high entry threshold: it is very detailed and takes a lot of time to figure out all the functionality. Price: 100% free
Shodan
You can find traffic lights, security cameras, home automation systems, heating systems—everything that is connected to the Internet—with the help of this software for OSINT.
For example, Shodan discovers a control system for a gas station, an amusement park, and even a wine fridge in one of the hotels. Moreover, it sounds a little scary, but OSINT experts have discovered nuclear power plants’ command and control systems and an atomic particle accelerator. The fact that most of these devices are not protected deserves special attention.
Link to the official website – https://developer.shodan.io/pricing
Pros:
- Has intuitive interface
- Displays metrics along with a geographic map
- Exports results and the ability to create reports
Cons:
- It’s not free
Price: As a Shodan user, you can choose from three different versions of the platform:
- Freelancer ($59/month)
- Small Business ($299/month)
- Corporate ($899/month)
Maltego

Maltego is software used for OSINT and computer forensics. It allows users to extract valuable information from the Internet and visualize the obtained data for effective link analysis. It can also discover connections between people and companies and search for publicly available information. For example, Maltego can find links between emails, usernames, companies, websites, etc.
Link to the official website – https://www.maltego.com/
Pros:
- A great tool for charting complex networks and relationships.
- It highlights a relationship between data points. You can add new sources through the API.
- There is a free version.
Cons:
- Quite expensive fees: price starts from $999
Price: Pricing Plans
theHarvester
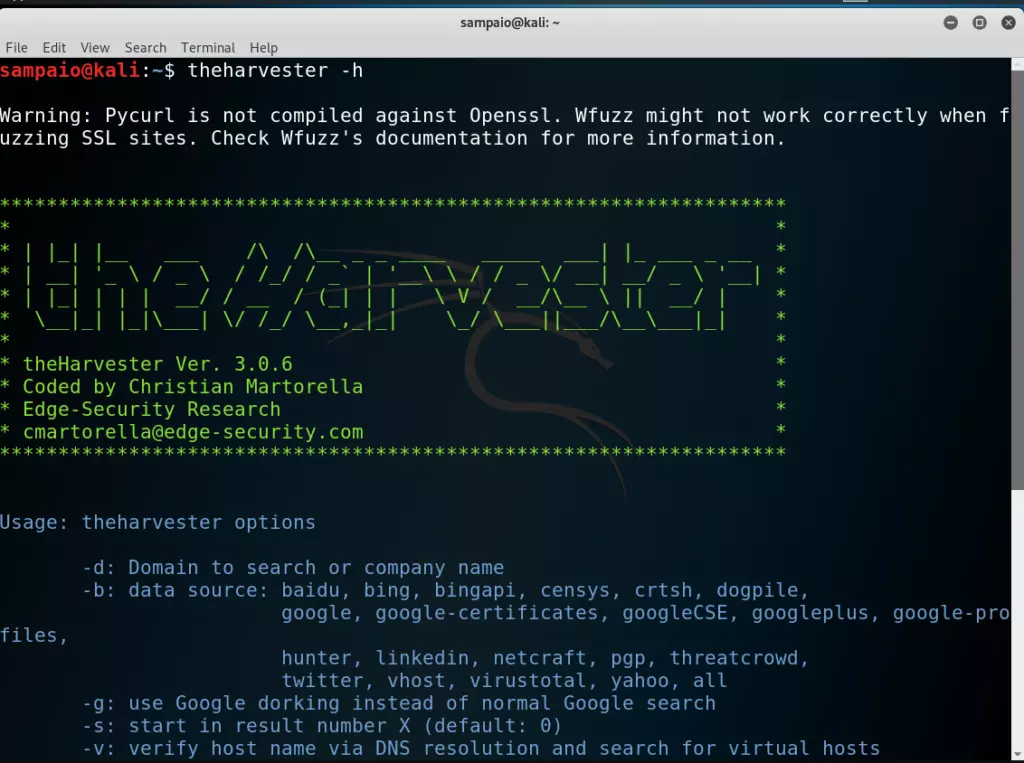
theHarvester is a simple OSINT passive intelligence tool written in Python. In addition to looking for information outside the organization, it can be used to find vulnerabilities inside it.
This tool can help you determine who uses or has used your domain name. It looks at public records to get information about your domain’s subdomains, URLs, IP addresses, email addresses, employee names, and more.
Link to the official site – https://tools.kali.org/information-gathering/theharvester
Pros:
- Free
- Simple
- Supported by a large number of like-minded people
Cons:
- No visualization
Price: Free
Recorded Future

Recorded Future is software that allows you to collect and analyze large amounts of threat data in real-time.
You can use this software to understand threats in your industry. In addition, you will be able to predict possible future threats for your company with its help. This action is necessary to develop means of protection and be ready for anything that can happen.
For example, Recorded Future collects data from public sources such as domain registrations, social media profiles, and third-party websites by using machine learning, artificial intelligence, and natural language processing technologies.
Link to the official website – https://www.recordedfuture.com/
Pros:
- The user interface is very simple.
- You can easily customize your dashboard with additional widgets.
- You can use collected threat information and other publicly available information for threat analysis.
Cons:
You need to contact the company to see its prices.
Price: Recorded Future has three different editions: Express, Core, and Advanced. Contact it for pricing information.
Metagoofil

This is an absolutely free Python tool for passive OSINT intelligence. You can extract metadata from doc, xls, pdf, and other files with it. At the same time, it can analyze publicly available documents on any web resource.
Metagoofil searches documents and downloads them to your computer to analyze and extract the data. If you need to find emails, servers, real usernames, or software versions, Metagoofil will do the job just fine.
Link to the official website – http://www.edge-security.com/metagoofil.php
Pros:
- has a wide choice of report export, including PDF
- finds and loads public tools
- is free
- has open source
- allows to set up filters (username, email address, and passwords)
Cons:
- is primitive in terms of visualization
Price: free
Searchcode
A unique search engine that allows you to search for information in open source. It can also be used to find privacy-related issues in your organization.
The engine works similarly to most search engines, but instead of web servers, it scans data in running applications or those still in development.
It helps a hacker identify vulnerabilities, find usernames, and more. Searchcode also analyzes code in repositories such as Bitbucket, GitHub, Google Code, etc.
Link to the official website – https://searchcode.com/
Pros:
- has simple interface
- has filters by language, phrase, or repository
- is free
Cons:
- there are no cons
Price: free
GHDB
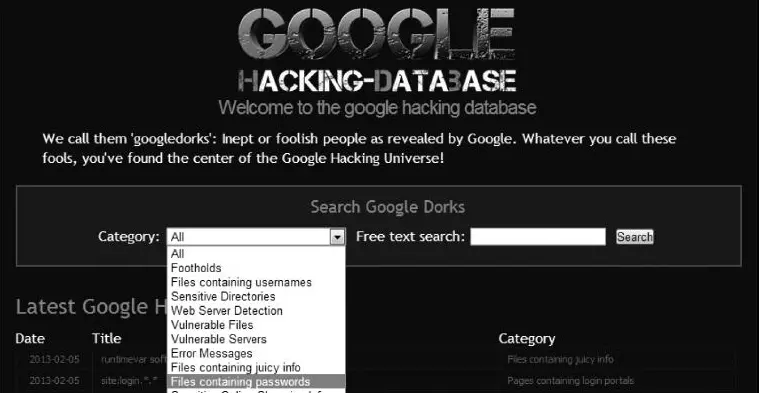
This service is often called Google Dorks, and, in fact, it is a database of special search queries. They can be used to search for publicly available information that a person might accidentally post on the Internet, including open ports, directories with confidential information, usernames, etc. Plus, the database is constantly updated.
If you understand how to create complex queries in Google, you can find vulnerabilities and breaches anywhere with the help of GHDB.
Link to the official website – https://www.exploit-db.com/google-hacking-database
Pros:
- has a huge community
- constantly evolving
- easy to use
Cons:
- Pages marked as “noindex” will not appear in a search result
Price: free
SpiderFoot
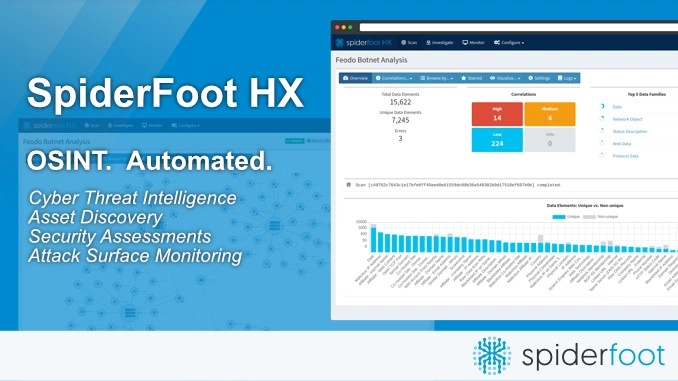
Spiderfoot is a tool for collecting data about e-mail addresses, domains, IPs, names, and how to track down phone numbers, among other things. You can connect to services like Shodan, Censys, and Have I Been Pwned using API keys.
SpiderFoot is used for automated reconnaissance. Its purpose is to simplify the process of collecting information by automating the information-collecting stage and giving a rich set of data to determine the direction of the test. It can also be used to collect information about suspicious and malicious IPs.
Spiderfoot is available for Windows and Linux.
Link to the official website – https://www.spiderfoot.net/
Pros:
- simple and user-friendly interface
- suitable for an extensive search
- completely free
- many modules for data collection
Cons:
- Pages marked as “noindex” will not appear in a search result
Price: free
OSINT Framework
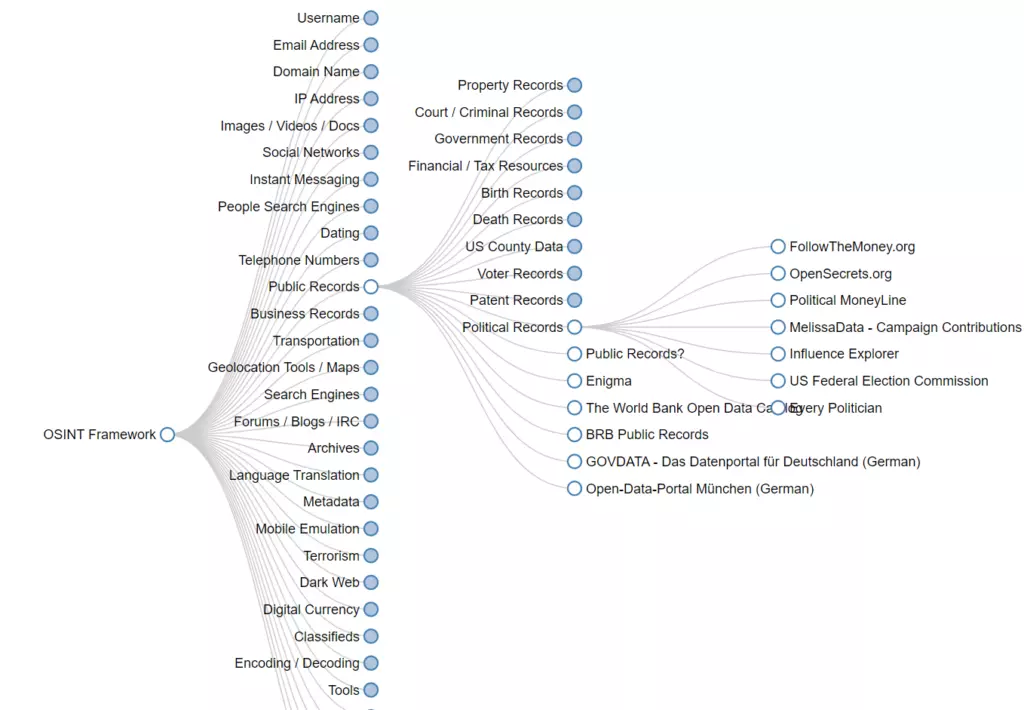
It is a guide to help you find your perfect OSINT intelligence tool if you haven’t found it yet. In fact, this is not a tool but an interactive information map. The usage is intuitive, and the information is perfectly organized. This software for OSINT is popular with cybersecurity professionals looking for tools for specific tasks.
Link to the official website – https://osintframework.com/
Pros:
- perhaps the best framework in the OSINT community
- many constantly updated tools
- convenient search by category
- absolutely free
Cons:
- there are no cons
Conclusion
OSINT will help you achieve cybersecurity in the organization and protect those areas outside of it. Understanding what information about you can be found in the public domain will allow you to protect yourself from passive intelligence and prevent or significantly reduce the risk of a full-scale attack.


