What is the OSINT framework? How to use the OSINT framework? Learn all you need to know in this OSINT framework tutorial.
How to Search With the OSINT framework
Information on the Internet is dissimilated through thousands of sites, documents, and web pages, most of which require various search techniques. However, in this case, collecting intelligence will take weeks if a person does not know what tools to use for different purposes, right? That’s when the OSINT framework comes to the rescue.
What is the OSINT framework?
You can use hundreds of different tools and techniques to find all kinds of information, but it’s very easy to get confused. The OSINT framework is an architecture that helps to avoid hours of searching for the desired program or site because its structure is already an ordered set of tools and sources. Of course, in the broadest sense of the OSINT framework, these are all possible techniques that help find information about the target more quickly and easily. However, in a narrower sense, it is a web platform in which different tools are classified and grouped depending on the purpose and approach to the search.
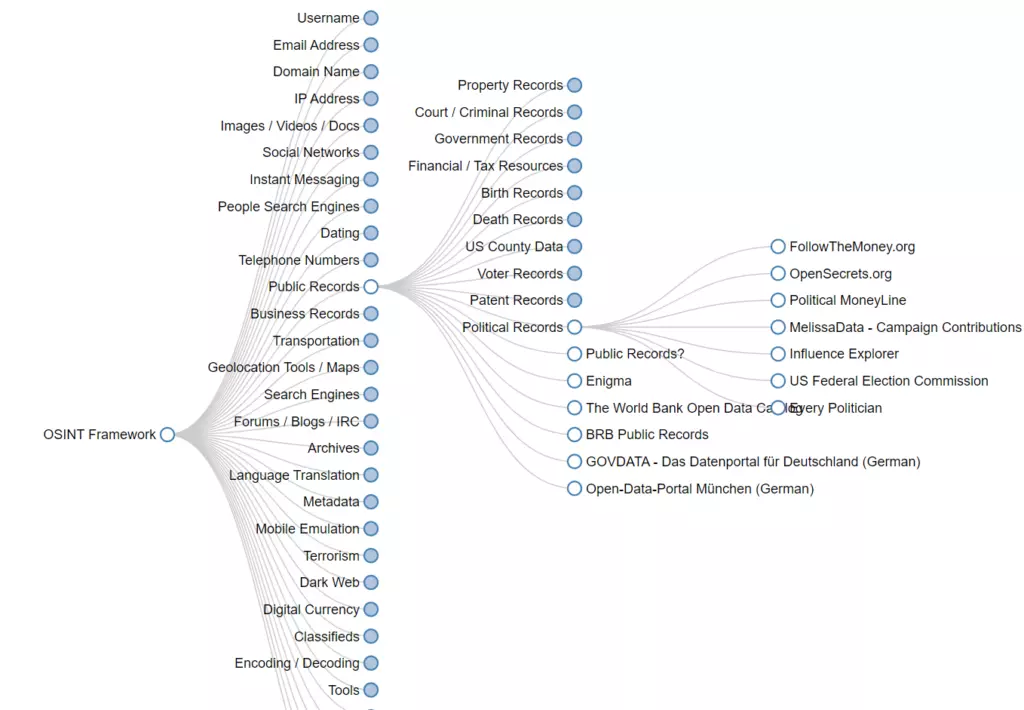
Classification of the OSINT framework
Let’s start with the fact that the OSINT framework consists of 32 different categories. They are:
- Training
- Documentation
- OpSec
- Threat Intelligence
- Exploits & Advisories
- Malicious File Analysis
- Tools
- Encoding / Decoding
- Classifieds
- Digital Currency
- Dark Web
- Terrorism
- Mobile Emulation
- Metadata
- Language Translation
- Archives
- Forums / Blogs / IRC
- Search Engines
- Geolocation Tools / Maps
- Transportation
- Business Records
- Public Records
- Telephone Numbers
- Dating
- People Search Engines
- Instant Messaging
- Social Networks
- Images / Videos / Docs
- IP Address
- Domain Name
- Email Address
- Username
Each category is divided into subcategories to clarify what kind of information or tool you need. If we start to describe each of them, we might write a short book, but we need to look at some of them.
Public Records
Although every private and public institution is required to store our data safely and securely, it often leaks during hacker attacks. Other data is stored in the public domain, and the main thing is to know in which databases you need to look for it. That is why the category has so many subcategories, namely:
- Political Records
- Patent Records
- Voter Records
- US County Data
- Death Records
- Birth Records
- Financial / Tax Resources
- Government Records
- Court / Criminal Records
- Property Records
The structure extracts some sources separately if they fall into several categories at once. In this case, there are Open-Data-Portal München (Germany), GOVDATA – Das Datenportal für Deutschland (Germany), BRB Public Records, The World Bank Open Data Catalog, Public Records?, and Enigma.
Others are sorted by category. For example, in Political Records, you can find:
- US Federal Election Commission
- Influence Explorer
- MelissaData – Campaign Contributions
- Political MoneyLine
- OpenSecrets.org
- FollowTheMoney.org
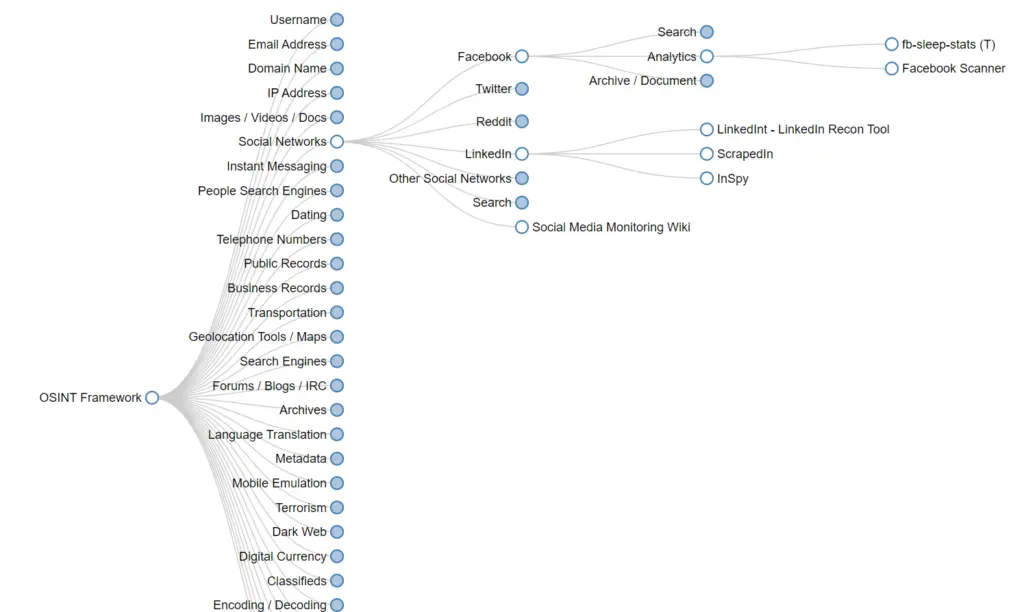
Social networks
Social networks are one of the first sources to be analyzed in data search, and the OSINT framework offers an impressive pool of tools for this purpose. The category is divided into subcategories representing all social networks, including Facebook, LinkedIn, Reddit, Twitter, and ten other sites popular in different countries. Then the subcategory can directly show the available tools like LinkedIn (InSpy, ScrapedIn, LinkedInt) or further specify the type of tools like Facebook (Analytics, Search, Archive / Document). In any case, in the end, you get a list of sites that will help you find all the necessary information on social networks.
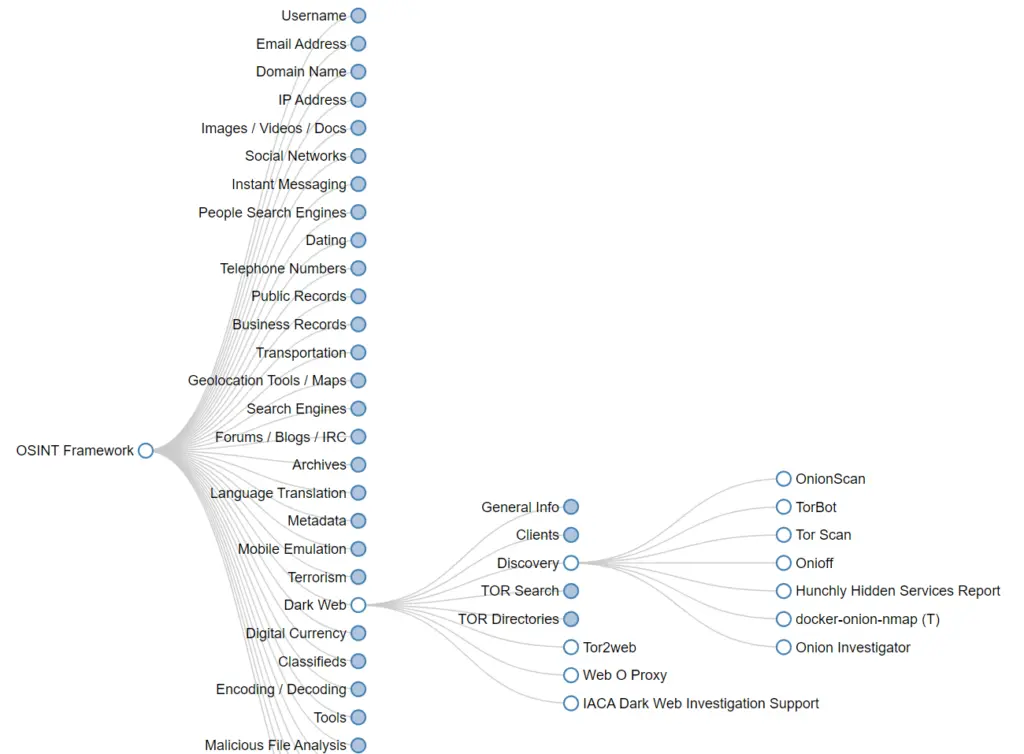
Dark Web
This category is a little contradictable, but sometimes you need to dive into the dark web to find what others hide there. You can find general information about the dark web or its clients and use TOR searches or TOR directories to dig into someone’s secrets. For example, the Directory subcategory offers such services as:
- Onion Investigator
- docker-onion-nmap (T)
- Hunchly Hidden Services Report
- Onioff
- Tor Scan
- TorBot
- OnionScan
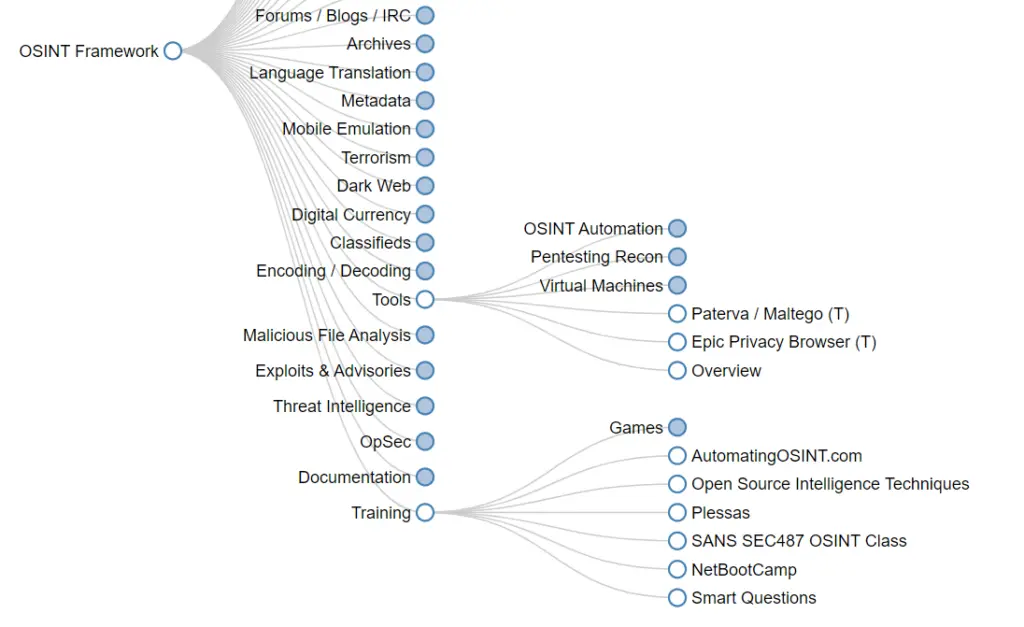
Additional tools
The OSINT framework also has a Tools category, which helps ease the process of collecting intelligence in general. It includes Pentesting Recon, OSINT Automation, and Virtual Machines subcategories, as well as links to Epic Privacy Browser, Paterva / Maltego (T), and their overview.
Other tools are in separate categories as they help with finding information when a specific person is not the target. For example, you can use malicious file analysis, OpSec, code analysis, or metadata analysis.
The framework also offers a separate category of OSINT learning resources in the form of games or text-based web pages.
X-Ray Contact is one convenient data aggregator that can help you identify a person from the database even if you have minimal data at the beginning, like name, phone number, photo or email. It can function both as an API for your system and as a separate tool.
Types of elements
You also need to know that all services or elements in structure are different in their accessibility and some other features. The OSINT framework made some indicators so customers could easily distinguish these characteristics.
(T) — this means that a user should download and install a tool via a link.
(D) — Google Dork (or Google Hacking).
(R) — a user should be registered.
(M) — shows that a customer needs to edit a URL manually and that it contains the search term.
So, mind that you need to make some additional moves if you see one of these letters next to the name of a service.
How to use the OSINT framework
So, it is pretty easy to use the OSINT framework as it is well-structured.
- Chose category you need based on the info you want to search
- Review subcategories and the one describing your search request the most clearly
- Repeat if there are more clarifying divisions
- Check if the provided services have one of the indicators and choose the most suitable one for you. You can come back later and use other services as well.
Conclusion
To sum up, the OSINT framework is an efficient and easy-to-use architecture as it includes most of the sources, tools, and links for data searching.
On the one hand, this framework helps choose the most convenient way or technique for collecting specific data. On the other hand, you can use it as a checklist so you don’t miss anything important in your intelligence-collecting process.
